Duo Two-Factor Authentication for LastPass
Last updated:
Overview
Duo protects access to your LastPass data by requiring approval when logging in to your LastPass Vault.
This application communicates with Duo's service on SSL TCP port 443.
Firewall configurations that restrict outbound access to Duo's service with rules using destination IP addresses or IP address ranges aren't recommended, since these may change over time to maintain our service's high availability. If your organization requires IP-based rules, please review Duo Knowledge Base article 1337.
Effective June 30, 2023, Duo no longer supports TLS 1.0 or 1.1 connections or insecure TLS/SSL cipher suites. See Duo Knowledge Base article 7546 for additional guidance.
First Steps
-
Log in to the Duo Admin Panel and navigate to Applications → Application Catalog.
-
Locate the entry for LastPass with the "2FA" label in the catalog. Click the + Add button to create the application, and get your Client ID, Client secret, and API hostname. You'll need this information to complete your setup. See Protecting Applications for more information about protecting applications with Duo and additional application options.
Previously, the Client ID was called the "Integration key" and the Client secret was called the "Secret key".
Treat your secret key like a passwordThe security of your Duo application is tied to the security of your secret key (skey). Secure it as you would any sensitive credential. Don't share it with unauthorized individuals or email it to anyone under any circumstances!
-
No active Duo users can log in to new applications until you grant access. Update the User access setting to grant access to this application to users in selected Duo groups, or to all users. Learn more about user access to applications. If you do not change this setting now, be sure to update it so that your test user has access before you test your setup.
This setting only applies to users who exist in Duo with "Active" status. This does not affect application access for existing users with "Bypass" status, existing users for whom the effective Authentication Policy for the application specifies "Bypass 2FA" or "Skip MFA", or users who do not exist in Duo when the effective New User Policy for the application allows access to users unknown to Duo without MFA.
Duo Universal Prompt
The Duo Universal Prompt provides a simplified and accessible Duo login experience for web-based applications, offering a redesigned visual interface with security and usability enhancements.
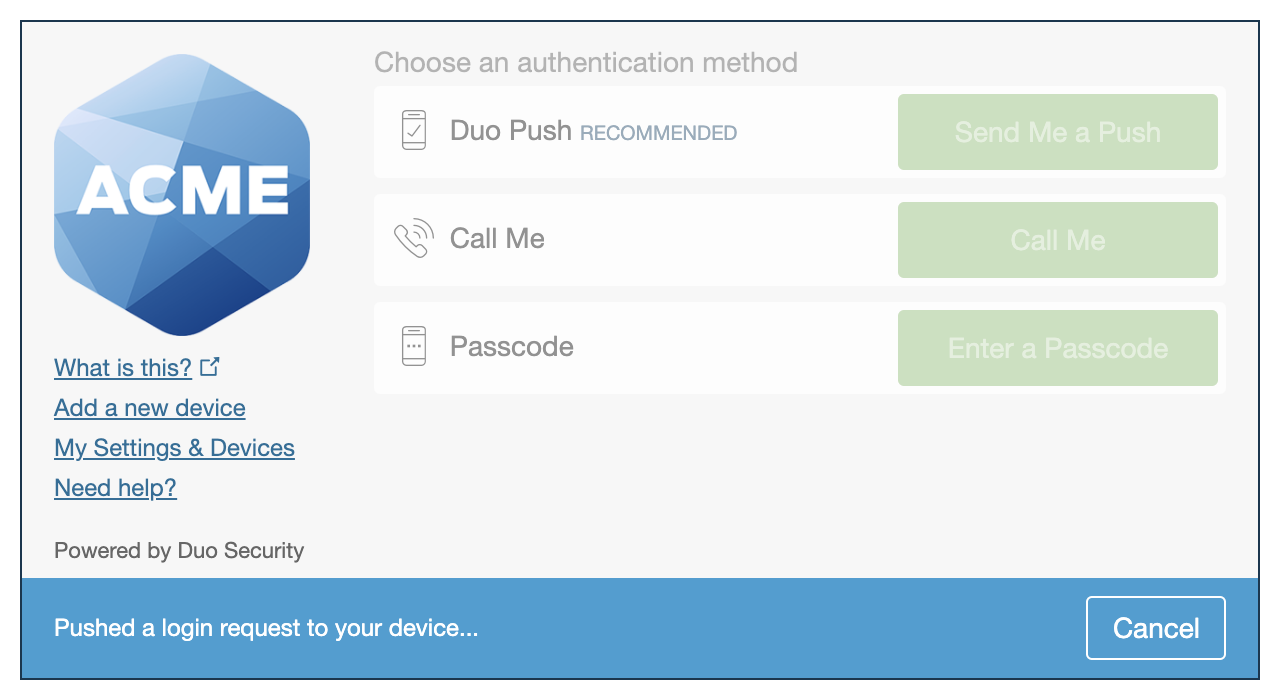
| Universal Prompt | Traditional Prompt |
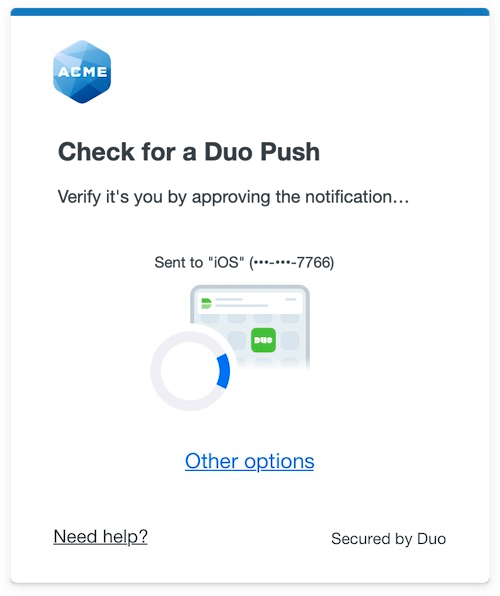 |
 |
LastPass has already updated their hosted Duo LastPass application to support the Universal Prompt, so there's no installation effort required on your part to update the application itself. If you're setting up Duo with LastPass for the first time you the Universal Prompt experience is already activated in the Duo Admin Panel.
If you already use Duo with LastPass you need to make a configuration change in LastPass, and then log in with Duo 2FA again so that Duo makes the Universal Prompt activation setting available in the Admin Panel. This first authentication after updating the LastPass setting shows the traditional Duo prompt in a redirect instead of an iframe. After that, activate the Universal Prompt experience from the Duo Admin Panel for users of that Duo LastPass application if the traditional prompt is still selected.
If you created your LastPass application before March 2024, it's a good idea to read the Universal Prompt Update Guide for more information, about the update process and the new login experience for users, before you activate the Universal Prompt for your application.
New LastPass Applications
When you configure Duo in LastPass for the first time, you're ready to use the Universal Prompt. LastPass applications created after March 2024 have the Universal Prompt activated by default. If you're configuring LastPass now, proceed with the installation instructions in this document.
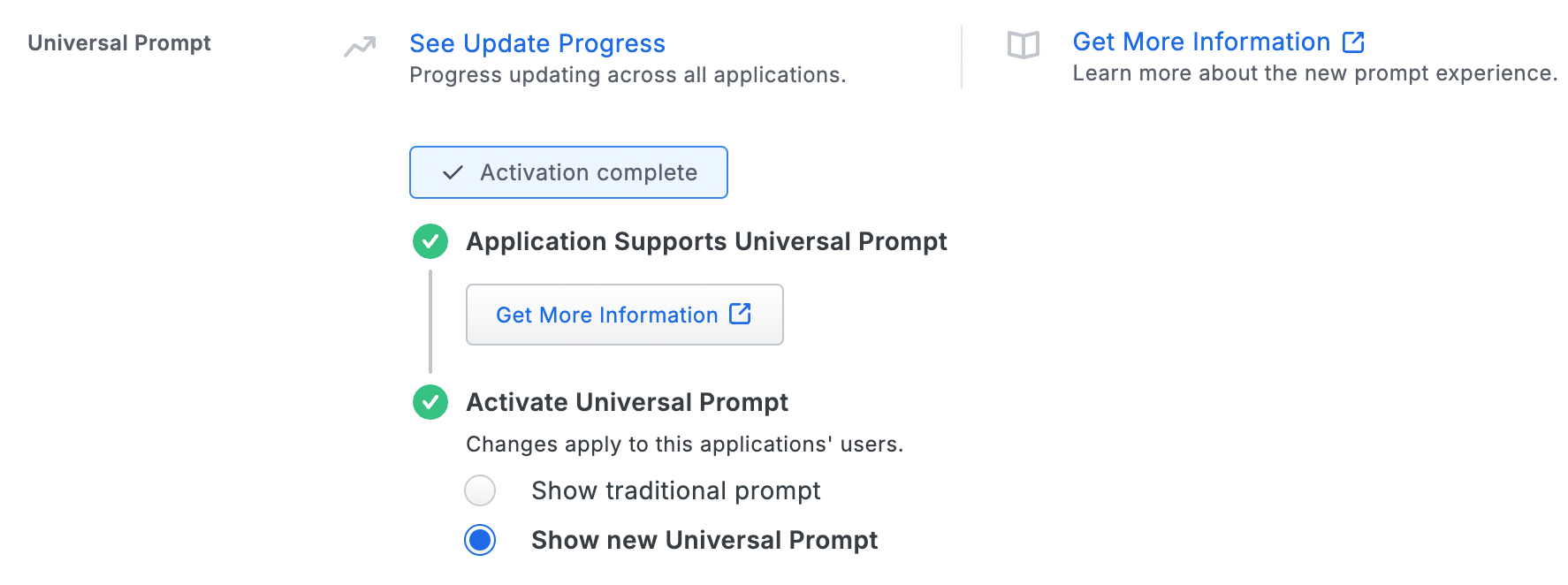
The "Universal Prompt" area of the application details page shows this application as "Activation complete", with these activation control options:
- Show traditional prompt: Your users experience Duo's traditional prompt via redirect when logging in to this application.
- Show new Universal Prompt: (Default) Your users experience the Universal Prompt via redirect when logging in to this application.
Existing LastPass Applications
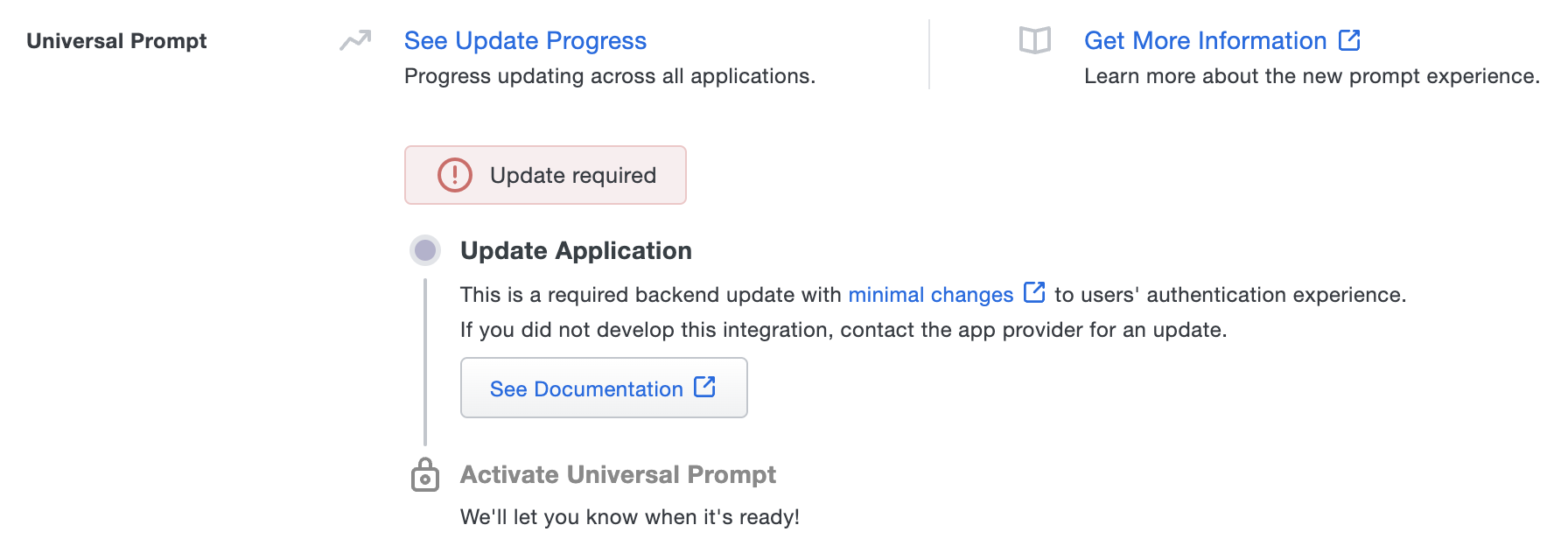
You'll need to make a configuration change in LastPass to use the Universal Prompt. The "Universal Prompt" section reflects this status as "Update required" today. To update the LastPass configuration, follow the directions below.
Activate Universal Prompt
Activation of the Universal Prompt is a per-application change. Activating it for one application does not change the login experience for your other Duo applications.
Once a user authenticates to the updated LastPass, the "Universal Prompt" section of the LastPass application page reflects this status as "Ready to activate", with these activation control options:
- Show traditional prompt: (Default) Your users experience Duo's traditional prompt when logging in to this application.
- Show new Universal Prompt: Your users experience the Universal Prompt via redirect when logging in to this application.

In addition, the "Integration key" and "Secret key" property labels for the application update to "Client ID" and "Client secret" respectively. The values for these properties remain the same.
Enable the Universal Prompt experience by selecting Show new Universal Prompt if the traditional prompt is still selected, and then scrolling to the bottom of the page to click Save.
Once you activate the Universal Prompt, the application's Universal Prompt status shows "Activation complete" here and on the Universal Prompt Update Progress report.
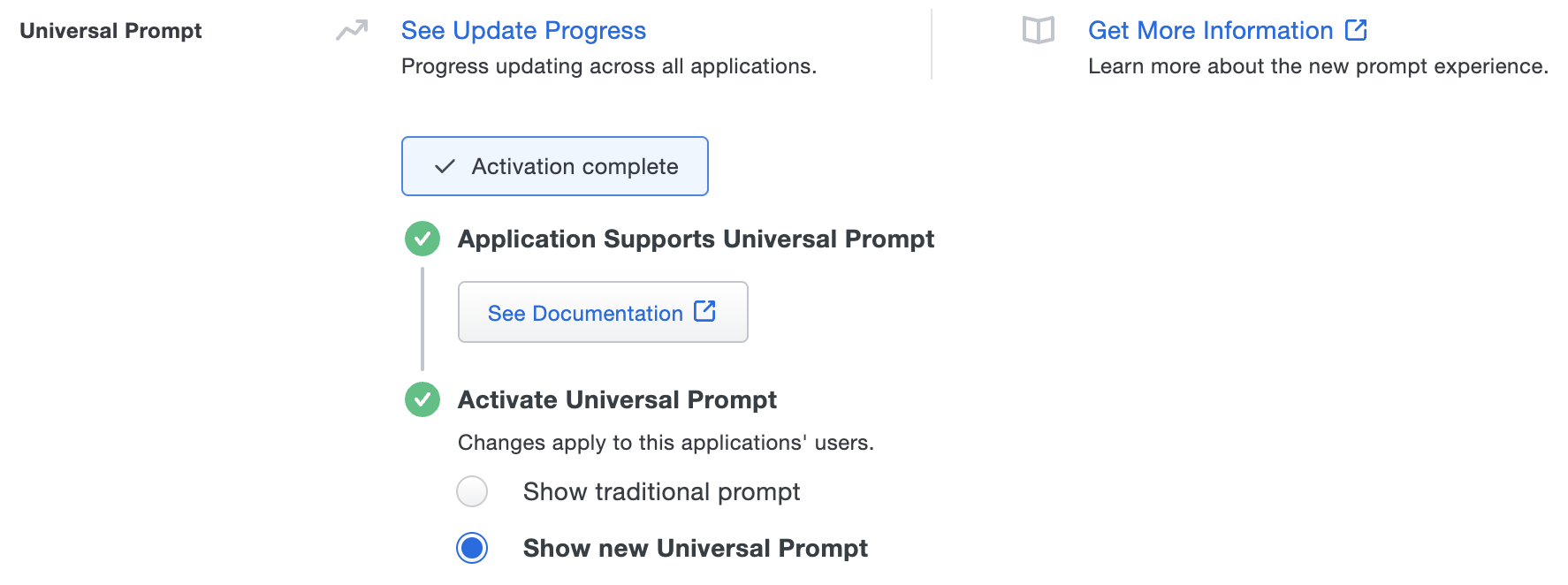
Should you ever want to roll back to the traditional prompt, you can return to this setting and change it back to Show traditional prompt. However, this will still deliver the Duo prompt via redirect, not in an iframe. Keep in mind the September 30, 2024 end-of-extended-support date for the traditional Duo prompt in LastPass applications.
Universal Update Progress
Click the See Update Progress link to view the Universal Prompt Update Progress report. This report shows the update availability and migration progress for all your Duo applications. You can also activate the new prompt experience for multiple supported applications from the report page instead of visiting the individual details pages for each application.
Enable Duo Web SDK
Visit your LastPass Admin Console to enable the Use Duo Web SDK when possible setting in your Duo multifactor authentication settings or enterprise policy so that web and browser extension logins to LastPass use the Duo Universal Prompt. Users of the LastPass browser extension should update to version 4.129 or later.
Configure Duo in LastPass Teams or Business
Be sure to enable the Use Duo Web SDK when possible option in your multifactor authentication policy so that web and browser extension logins to LastPass use the Duo Universal Prompt. Users of the LastPass browser extension should update to version 4.129 or later.
Configure Duo in LastPass Personal Plans
Be sure to enable the Use Duo Web SDK when possible option in your multifactor options for Duo Security so that web and browser extension logins to LastPass use the Duo Universal Prompt. Users of the LastPass browser extension should update to version 4.129 or later.
Test Your Setup
After completing multifactor setup, you'll see a Duo two-factor authentication prompt when you log in to LastPass. Follow the instructions shown to log in.
LastPass Web Page and Browser Extension
The LastPass Duo multifactor window displays after entering your username and password. If you enabled the "Use Duo Web SDK when possible" setting, then you'll see an Authenticate button.
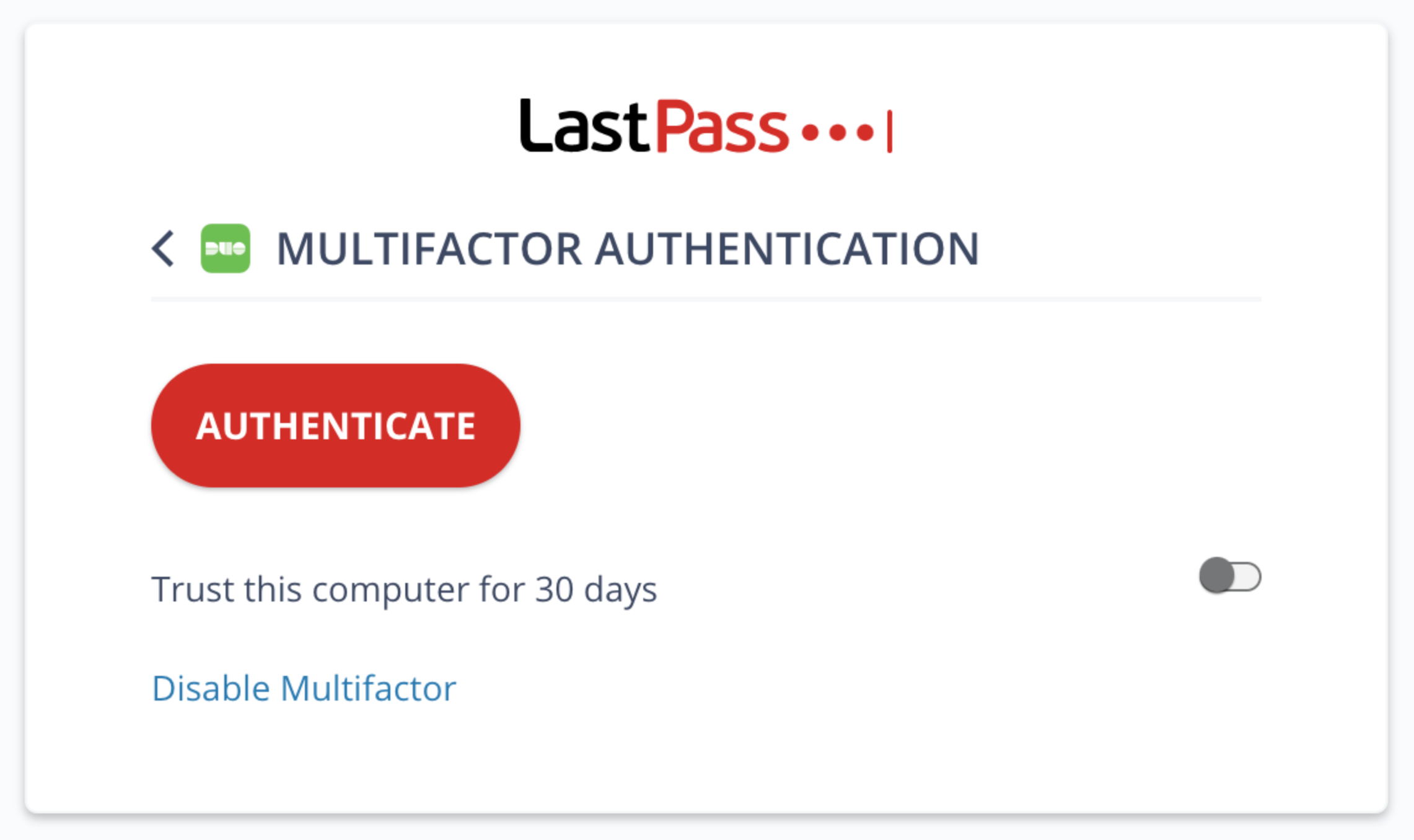
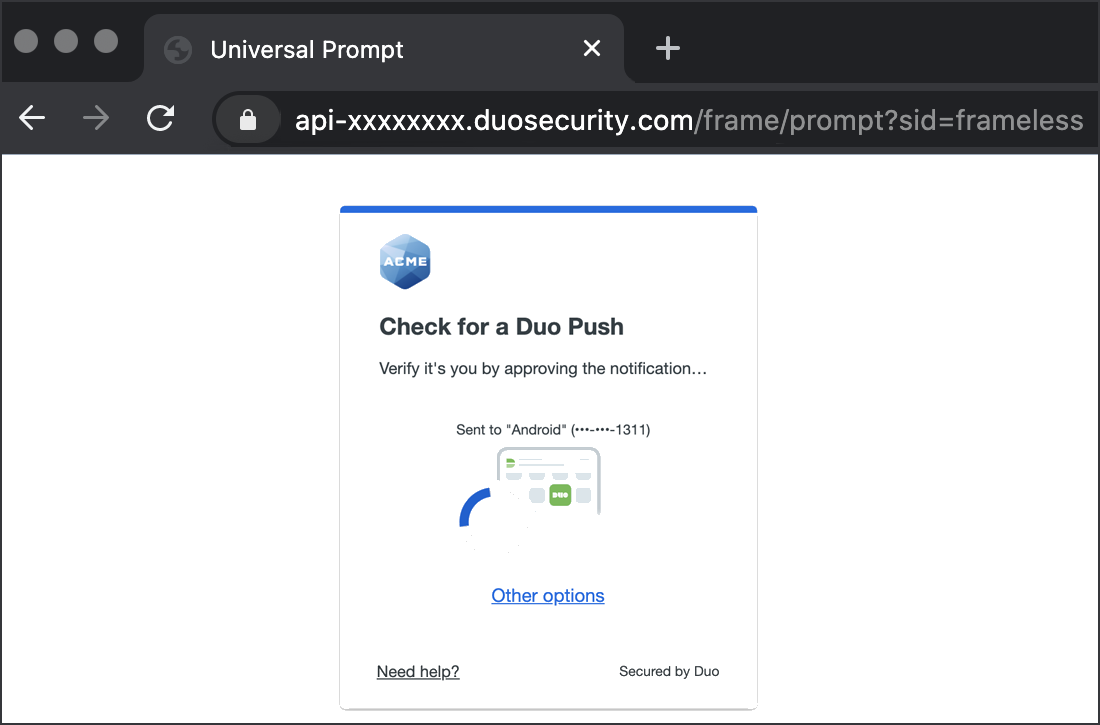
Clicking the Authenticate button redirects you to Duo to complete two-factor authentication. You'll return to LastPass to complete the login process after successful Duo authentication.
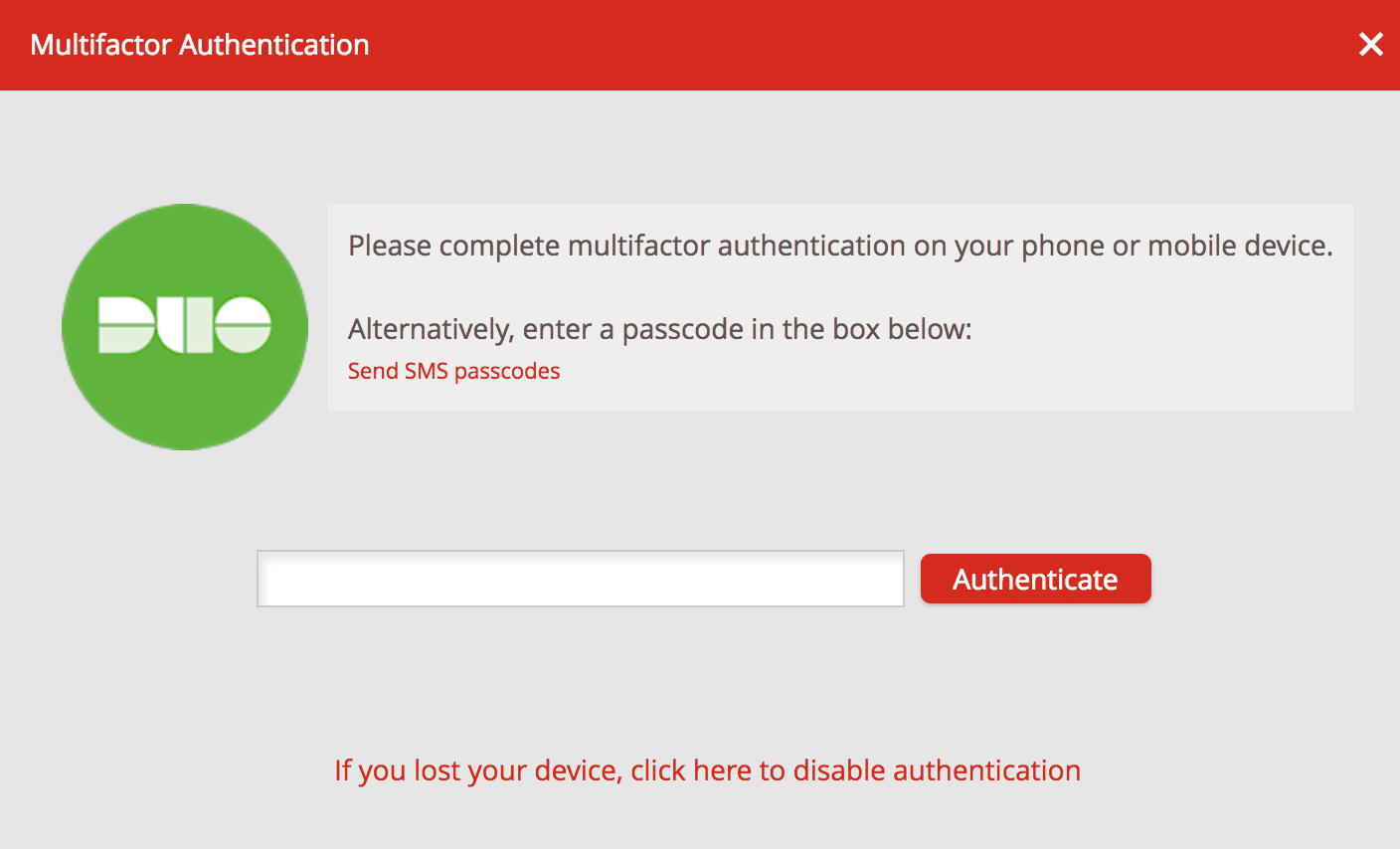
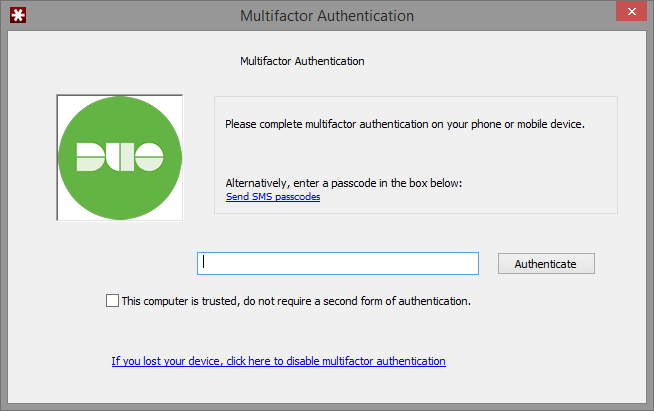
If you left the "Use Duo Web SDK when possible" option at the default "No" setting, then you'll see the LastPass Duo prompt and at the same time a push authentication request appears on your mobile device if you've activated Duo Mobile.
If you click the "This computer is trusted..." option then you won't be prompted for two-factor authentication again from the same browser on that device.
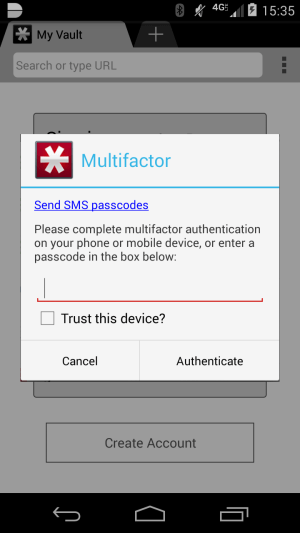
LastPass Mobile App
The LastPass Duo multifactor window displays after entering your username and password in the LastPass for Applications login window, and at the same time a push authentication request appears on your mobile device if you've activated Duo Mobile. You may approve the Duo Push request from the same device where you are logging into the LastPass mobile app.
If you click the "Trust this device?" option then you won't be prompted for two-factor authentication again by the LastPass app on that device.
LastPass for Applications
The LastPass for Applications program is available for Microsoft Windows only. The LastPass Duo multifactor window displays after entering your username and password in the LastPass for Applications login window, and at the same time a push authentication request appears on your mobile device if you've activated Duo Mobile.
If you click the "This computer is trusted..." option then you won't be prompted for two-factor authentication again when logging in to LastPass for Applications.
Grant Access to Users
If you did not already grant user access to the Duo users you want to use this application be sure to do that before inviting or requiring them to log in with Duo.
Troubleshooting
Need some help? Reach out to Duo Support for assistance with creating the LastPass application in Duo, enrolling users in Duo, Duo policy questions, or Duo authentication approval issues. For assistance configuring or managing LastPass please contact LastPass support.
